COMPUTER SCIENCE AND ENGINEERING (CYBER SECURITY)
Program: B.Tech. in Computer Science and Engineering (Cyber Security)
Year of establishment: 2024
Duration: 4 Years
Year of Commencement: 2024
Current Intake: 60
B.Tech in Computer Science and Engineering (Cyber Security) is an undergraduate 4 years program that integrates fundamental concepts of computer science with specialized knowledge in securing digital systems, networks, and data. The curriculum includes core subjects such as programming, data structures, and operating systems, along with advanced topics like cryptography, ethical hacking, network security, and digital forensics.
The program emphasizes both theoretical understanding and practical skills, enabling students to identify vulnerabilities, analyze cyber threats, and implement effective security solutions. Graduates are well-prepared for roles such as cybersecurity analyst, ethical hacker, and digital forensic expert, contributing to the protection of information systems across various industries.

A graduate of Computer Science and Engineering (Cyber Security) will be able to:
| Program Outcomes (POs) | Statement |
|---|---|
| PO1 | Engineering Knowledge: Apply the knowledge of mathematics, science, engineering fundamentals, and an engineering specialization for the solution of complex engineering problems. |
| PO2 | Problem Analysis: Identify, formulate, research literature, and analyze complex engineering problems reaching substantiated conclusions using first principles of mathematics, natural sciences, and engineering sciences. |
| PO3 | Design/ Development of Solutions: Design solutions for complex engineering problems and design system components or processes that meet the specified needs with appropriate consideration for public health and safety, and cultural, societal, and environmental considerations. |
| PO4 | Conduct Investigations of Complex Problems: Use research-based knowledge and research methods including design of experiments, analysis and interpretation of data, and synthesis of the information to provide valid conclusions. |
| PO5 | Modern Tool Usage: Create, select, and apply appropriate techniques, resources, and modern engineering and IT tools including prediction and modeling to complex engineering activities with an understanding of the limitations. |
| PO6 | The Engineer and Society: Apply reasoning informed by the contextual knowledge to assess societal, health, safety, legal, and cultural issues and the consequent responsibilities relevant to the professional engineering practice. |
| PO7 | Environment and Sustainability: Understand the impact of the professional engineering solutions in societal and environmental contexts, and demonstrate the knowledge of, and need for sustainable development. |
| PO8 | Ethics: Apply ethical principles and commit to professional ethics and responsibilities and norms of the engineering practice. |
| PO9 | Individual and Teamwork: Function effectively as an individual, and as a member or leader in diverse teams, and in multidisciplinary settings. |
| PO10 | Communication: Communicate effectively on complex engineering activities with the engineering community and with the society at large, such as being able to comprehend and write effective reports and design documentation, make effective presentations, and give and receive clear instructions. |
| PO11 | Project Management and Finance: Demonstrate knowledge and understanding of the engineering and management principles and apply these to one’s own work, as a member and leader in a team, to manage projects and in multidisciplinary environments. |
| PO12 | Life-Long Learning: Recognize the need for, and have the preparation and ability to engage in independent and life-long learning in the broadest context of technological change. |
| Program Outcomes (POs) | Statement | Knowledge and Attitude Profile |
|---|---|---|
| PO1 | Engineering Knowledge: Apply knowledge of mathematics, natural science, computing, engineering fundamentals and an engineering specialization as specified in WK1 to WK4 respectively to develop to the solution of complex engineering problems. | WK1, WK2, WK3. WK4 |
| PO2 | Problem Analysis: Identify, formulate, research literature, and analyze complex engineering problems reaching substantiated conclusions using first principles of mathematics, natural sciences, and engineering sciences. | WK1, WK2, WK3, WK4 |
| PO3 | Design/ Development of Solutions: Design solutions for complex engineering problems and design system components or processes that meet the specified needs with appropriate consideration for public health and safety, and cultural, societal, and environmental considerations. | WK5 |
| PO4 | Conduct Investigations of Complex Problems: Use research-based knowledge and research methods including design of experiments, analysis and interpretation of data, and synthesis of the information to provide valid conclusions. | WK8 |
| PO5 | Engineering Tool Usage: Create, select and apply appropriate techniques, resources and modern engineering & IT tools, including prediction and modelling recognizing their limitations to solve complex engineering problems. | WK2, WK6 |
| PO6 | The Engineer and The World: Analyze and evaluate societal and environmental aspects while solving complex engineering problems for its impact on sustainability with reference to economy, health, safety, legal framework, culture and environment. | WK1, WK5, WK7 |
| PO7 | Ethics: Apply ethical principles and commit to professional ethics, human values, diversity and inclusion; adhere to national & international laws. | WK9 |
| PO8 | Individual and Collaborative Team work: Function effectively as an individual, and as a member or leader in diverse/multi-disciplinary teams. | |
| PO9 | Communication: Communicate effectively and inclusively within the engineering community and society at large, such as being able to comprehend and write effective reports and design documentation, make effective presentations considering cultural, language, and learning differences | |
| PO10 | Project Management and Finance: Apply knowledge and understanding of engineering management principles and economic decision-making and apply these to one’s own work, as a member and leader in a team, and to manage projects and in multidisciplinary environments. | |
| PO11 | Life-Long Learning: Recognize the need for, and have the preparation and ability for i) independent and life-long learning ii) adaptability to new and emerging technologies and iii) critical thinking in the broadest context of technological change. | WK8 |
Ignite and nurture young learners to provide a sustainable, humane, and research-centric educational platform in the domain of cybersecurity for building a robust, resilient, and attack-free digital universe



DR. GOUR SUNDAR MITRA THAKUR
B.Tech, M.Tech, Ph.D.
Contact No:
Contact Email: gour.mitrathakur@bcrec.ac.in
Welcome to the Department of Computer Science and Engineering (Cyber Security)! We are delighted to welcome you to a field that stands at the forefront of safeguarding the digital world.
We live in an age where technology connects people, systems, and organizations on an unprecedented scale. As digital transformation continues to reshape every sector of society, the need to protect information, preserve privacy, and defend critical infrastructures has become more important than ever. Cyber Security is no longer just a specialized discipline; it is a vital foundation for trust, resilience, and progress in the modern world.
At Dr. B. C. Roy Engineering College, Durgapur, our department is committed to preparing students to meet these emerging challenges with knowledge, integrity, and confidence. We offer a strong academic foundation, practical exposure to real-world security issues, and an environment that encourages analytical thinking, innovation, and responsible technological leadership.
Through a carefully designed curriculum, hands-on learning opportunities, and engagement with current tools and practices, we aim to equip our students with the skills needed to identify vulnerabilities, counter cyber threats, secure digital ecosystems, and contribute meaningfully to a safer technological future.
Whether your aspiration is to become a cyber security analyst, ethical hacker, security architect, researcher, or innovator, the education and experience you gain here will empower you to play a critical role in protecting the digital society of tomorrow.
Join us in this exciting journey of learning, exploration, and innovation. Together, let us build the expertise, resilience, and vision required to secure the future in an increasingly interconnected world.
Your future begins here. Embrace the opportunities ahead, and let us guide you toward excellence and success.
| Dr, Subir Panja | Associate Professor |
| DR. SOHAM BANDYOPADHYAY | Assistant Professor |
| Sudipta Samanta | Assistant Professor |
| Amit Mondal | Assistant Professor |
1. Research Excellence & Scholarly Contributions
Our faculty members are actively engaged in high-quality research and innovation across emerging domains such as Artificial Intelligence, Machine Learning, Healthcare Analytics, and Data Science. Their work combines strong theoretical foundations with practical relevance, addressing real-world challenges through data-driven approaches. They contribute through publications in reputed journals and international conferences, fostering academic excellence, interdisciplinary collaboration, and exposure to advanced technologies.
Publication details:
International Journal: 12 (Including SCI, SCIE, SCOPUS)
International Conference: 14 (Including Springer, IEEE)
Book Chapter: 1 (Elsevier)
Notable achievement:
“Cardiac Risk Factors Identification with Hybrid Statistical Approach and Prediction of Cardiovascular Disease with Machine Learning”, which was presented at the IEEE International Conference on Information Technology (OCIT 2023), National Institute of Technology Raipur.
2. Faculty Development & Continuous Learning
Faculty members have collectively participated in 22+ Faculty Development Programs (FDPs)
3. Awards, Recognition & Academic Distinction
4. Leadership, Coordination & Institutional Contributions
The High-Performance Cyber Security Lab is designed to support advanced computing and security experiments using modern high-performance systems. It enables the analysis of large-scale data, simulation of cyber-attacks, and development of intelligent security solutions within a safe and controlled environment.
While the lab primarily focuses on cyber security, it also promotes multidisciplinary research by integrating machine learning (ML) and deep learning (DL) techniques for security analysis and robust model development. In addition, the lab emphasizes the design of secure architectures for medical and healthcare data, ensuring privacy, reliability, and trustworthy decision-making in sensitive data-driven applications. This combination of cyber security and intelligent data analysis broadens the scope of research toward real-world, high-impact domains. The lab facilities of the department are as follows:
Intrusion Detection 
Detect and prevent cyber attacks using machine learning techniques.
Network Anomaly Detection
Identify unusual or suspicious activities in network traffic.
DDoS Attack Simulation
Study large-scale attacks and evaluate system protection strategies. 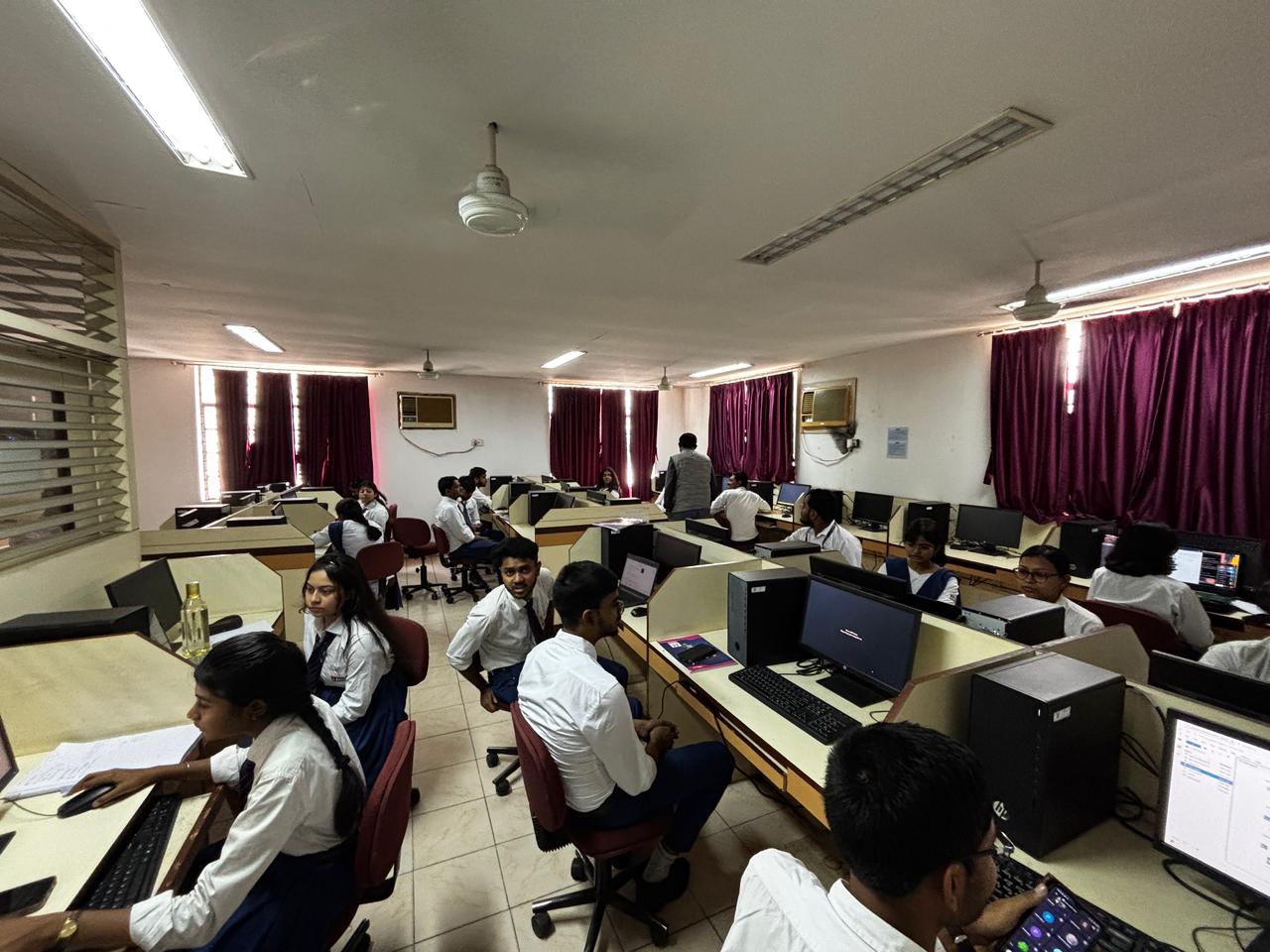
IoT Security
Ensure secure communication among interconnected smart devices.
ML/DL-Based Model Security & Explainability (Human-Centric Data)
Analyze and secure machine learning and deep learning models by extracting critical features from human-centric neural and biological datasets, while incorporating explainable AI techniques to ensure transparent, reliable, and trustworthy decision-making.
Log Analysis Lab 
Examine system logs to detect hidden vulnerabilities and cyber threats.
| Date | Name | Description | DOI | Link |
|---|---|---|---|---|
| 01-02-2026 | Dr, Subir Panja | Fuzzy-logic-based IoMT framework for COVID19 patient monitoring : Subir Panja, Arup Kumar Chattopadhyay, Amitava Nag, Jyoti Prakash Singh : Computers & Industrial Engineering | DOI | View |
| 08-12-2025 | DR. SOHAM BANDYOPADHYAY | Decoding brain tumors: an attention-guided hybrid learning framework for multi-class classification of MRI images : Soham Bandyopadhyay, Arnab Banerjee, Bhumik Roy, Ankur Lodh : International Journal of Information Technology | DOI | View |
| 01-04-2025 | DR. SOHAM BANDYOPADHYAY | AI-enabled computational intelligence approach to neurodevelopmental disorders detection using rs-fMRI data : S Bandyopadhyay, M Sarma, D Samanta : Computers and Electrical Engineering | DOI | View |
| 05-03-2025 | DR. SOHAM BANDYOPADHYAY | Novel framework of significant risk factor identification and cardiovascular disease prediction : Soham Bandyopadhyay a , Ananya Samanta b , Monalisa Sarma c , Debasis Samanta d : Expert Systems with Applications | DOI | View |
| 07-01-2025 | Dr, Subir Panja | An Efficient Malware Detection Approach Based on Machine Learning Feature Influence Techniques for Resource-Constrained Devices : SUBIR PANJA, SUBHASH MONDAL, AMITAVA NAG, JYOTI PRAKASH SINGH, MANOB JYOTI SAIKIA AND ANUP KUMAR BARMAN : IEEE ACCESS | DOI | View |
| 16-04-2024 | DR. SOHAM BANDYOPADHYAY | Tri‑fuzzy interval arithmetic with deep learning and hybrid statistical approach for analysis and prognosis of cardiovascular disease : Soham Bandyopadhyay, Monalisa Sarma, Debasis Samanta : International Journal of Information Technology | DOI | View |
| 14-04-2024 | DR. SOHAM BANDYOPADHYAY | SOHAM BANDYOPADHYAY Statistical Analysis of Renal Risk Factors and Prediction of Chronic Kidney Disease : Soham Bandyopadhyay, Monalisa Sarma, Debasis Samanta : SN Computer Science | DOI | View |
| 24-02-2024 | DR. SOHAM BANDYOPADHYAY | Decoding autism: Uncovering patterns in brain connectivity through sparsity analysis with rs-fmri data : S Bandyopadhyay, S Peddi, M Sarma, D Samanta : Journal of neuroscience methods | DOI | View |
| 13-07-2022 | Dr, Subir Panja | Lightweight CNN-based malware image classification for resource-constrained applications : Ashlesha Hota · Subir Panja · Amitava Nag : Innovations in Systems and Software Engineering | DOI | View |
| 08-06-2018 | DR. SOHAM BANDYOPADHYAY | Improving the Performance of Fuzzy Minimum Spanning Tree based Routing Process through PNode Fuzzy Multicasting Approach in MANET : Soham Bandyopadhyay, Sunil Karforma : I. J. Computer Network and Information Security | DOI | View |
| 08-03-2016 | DR. SOHAM BANDYOPADHYAY | Derivation and Comparative Study on Centroid Ranking Value of TrIFN and Apply on Fuzzy Geometric Programming : Soham Bandyopadhyay : I.J. Information Technology and Computer Science | DOI | View |
| Date | Name | Description | DOI | Link |
|---|---|---|---|---|
| 05-05-2026 | DR. SOHAM BANDYOPADHYAY | Energy-Optimized Sliding-Window Mutual Information-Powered Dynamic Functional Connectivity for Parkinson’s Disease Prediction : Soham Bandyopadhyay, Arnab Banerjee, Suman Dasgupta, Amit Mondal : IEEE International Conference on AI Engineering and Innovation (AIEI2026) | DOI | View |
| 29-07-2025 | DR. SOHAM BANDYOPADHYAY | Predicting ADHD: Combining Data-Driven ROI Extraction and Composite Graph Spectral Analysis : Soham Bandyopadhyay, M Unnikrishnan, Monalisa Sarma, Debasis Samanta : International Conference on Computer Vision and Image Processing | DOI | View |
| 21-04-2025 | DR. SOHAM BANDYOPADHYAY | Autism Spectrum Disorder Prediction Using Sparse Connectivity Patterns in RS-fMRI Data : Soham Bandyopadhyay, Santhoshkumar Peddi, Monalisa Sarma, Debasis Samanta : 2024 IEEE 21st India Council International Conference (INDICON) | DOI | View |
| 04-11-2024 | DR. SOHAM BANDYOPADHYAY | Prediction of neurodevelopmental disorder by combining data-driven ROI extraction and frequency specific brain functional connectivity approach : Soham Bandyopadhyay, Monalisa Sarma, Debasis Samanta : 2024 15th International Conference on Computing Communication and Networking Technologies (ICCCNT) | DOI | View |
| 19-02-2024 | DR. SOHAM BANDYOPADHYAY | Cardiac Risk Factors Identification with Hybrid Statistical Approach and Prediction of Cardiovascular Disease with Machine Learning : Soham Bandyopadhyay; Monalisa Sarma; Debasis Samanta : 2023 OITS International Conference on Information Technology (OCIT) | DOI | View |
| 11-12-2023 | DR. SOHAM BANDYOPADHYAY | Statistical analyses for key risk factor identification and prediction of chronic kidney disease : Ananya Samanta, Soham Bandyopadhyay, Debasis Samanta : 2023 45th Annual International Conference of the IEEE Engineering in Medicine & Biology Society (EMBC) | DOI | View |
The following activities highlight the academic, technical, and professional development initiatives undertaken by the students during the last academic year.
Seminars & Awareness Campaigns
Project SHIELD: Awareness Campaign on Nationwide Digital Fraud
Students participated in a nationwide initiative by the India Today Group and the International Fact-Checking Network to combat cyber and telecommunication fraud.
Gained insights into modern scams including digital arrest fraud, OTP theft, phishing, and AI-generated voice manipulation.
Engaged in live scam demonstrations and victim case studies conducted by experts from the India Today Fact Check Bureau.
Selected "Project SHIELD Champions" among students to foster digital safety within the campus community.
Learned critical reporting mechanisms through the national cybercrime portal and helpline 1930.
Cyber Attacks in Global Politics
Webinars
Full Stack Development (Euphoria GenX, Kolkata)
Technical Session on Engineering & Management Practices (Genex Engineering)
Workshops & Hands-on Training
20-Hour Hybrid Workshop: Full Stack Development using Django & React
PicPay: Image-to-product recognition and price comparison chatbot.
MindCare with StudyBuddy: AI-driven learning and mental wellness platform.
Bengali-Doctor: A bilingual healthcare chatbot.
OPTIBUY: AI-based device recommendation system.
DSA Chatbot: An AI assistant specifically for learning Data Structures and Algorithms.
Technical Clubs & Student Initiatives
Inauguration of "CODE_RED" Coding Club
The Department of CSE (CS) maintains a robust and dynamic interface with premier industrial organizations, ensuring that our academic framework remains deeply rooted in real-world application. By fostering consistent engagement with stalwarts such as the Durgapur Steel Plant (DSP), Damodar Valley Corporation (DVC), and CSIR-CMERI, the department creates a fertile ecosystem for technical evolution. These collaborations transcend traditional learning, as our students actively participate in intensive internships that provide them with a first-hand look at large-scale industrial operations and complex problem-solving.
Beyond internships, our department serves as a hub for knowledge exchange through regular interactions with seasoned industry resource persons. By collaborating on live industry projects, we integrate cutting-edge tools, sophisticated techniques, and professional methodologies directly into the students' academic journey. This proactive exposure acts as a powerful catalyst, motivating students to implement industry-standard concepts within their studies and future careers. Ultimately, this synergistic approach ensures that our graduates are not just academically proficient but are "industry-ready" professionals equipped with the resilience and technical acumen to thrive in a competitive global landscape.